The certificate industry has reached a pivotal moment. After extensive deliberation and multiple revisions, the CA/Browser Forum has officially approved a measure that will fundamentally transform how organizations manage Transport Layer Security certificates. The new regulations establish a clear roadmap toward 47-day certificate lifetimes, representing the most significant change in certificate management practices in over a decade.
This decision follows years of incremental reductions in certificate validity periods. The industry has been signaling this direction consistently, moving from multi-year certificates to the current maximum of 398 days. Now, with formal approval secured, organizations face a mandate rather than a recommendation. The change affects every entity that depends on TLS certificates to secure web servers, protect data transmissions, and maintain trust with clients.
Understanding the implications extends beyond technical implementation. This transformation demands strategic planning, resource allocation, and organizational readiness. Companies that prepare proactively will navigate the transition smoothly, while those waiting until deadlines approach risk service disruptions, security gaps, and compliance failures.
This comprehensive guide examines every aspect of the 47-day certificate lifetime mandate, from the technical timeline to implementation strategies, security benefits to cost considerations, and industry perspectives to future trends.
Understanding the 47-Day TLS Certificate Mandate
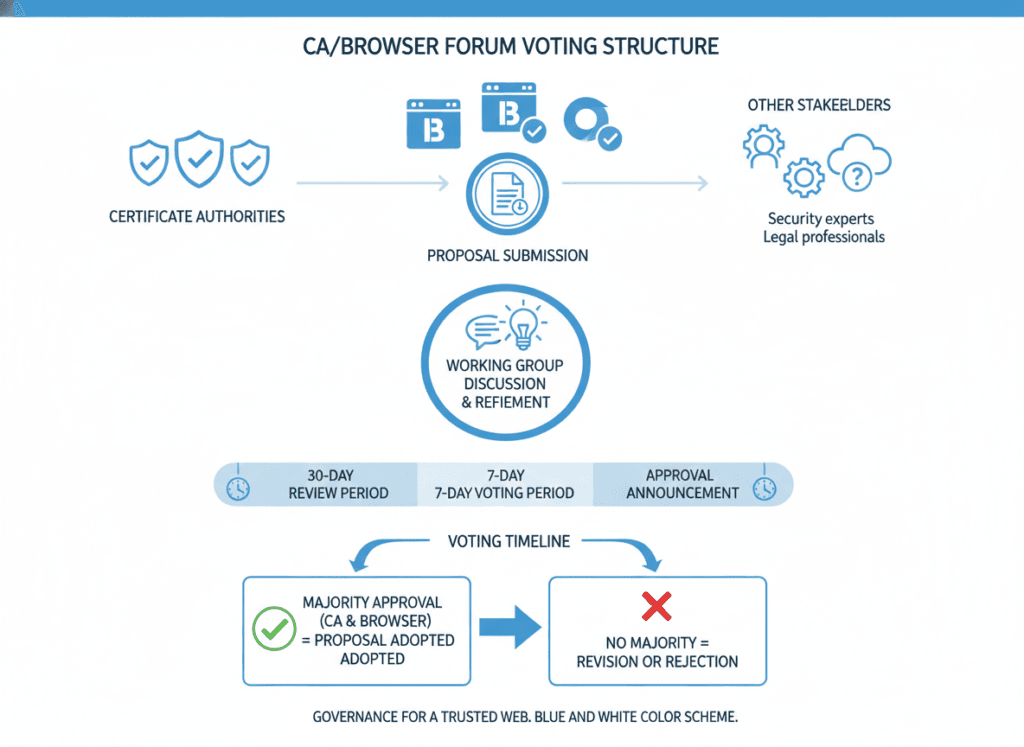
The CA/Browser Forum vote concluded on April 11, 2025, marking the end of a contentious debate that engaged certificate authorities, browser vendors, and enterprise stakeholders. The approved ballot establishes mandatory maximum lifetimes for Transport Layer Security certificates issued by publicly trusted certificate authorities. This represents binding industry policy rather than voluntary guidance.
The Legislative Process Behind the Decision
The ballot underwent several iterations before reaching final approval. Initial proposals sparked intense discussion within the certificate community, with various stakeholders advocating different approaches. Google initially championed a 90-day maximum lifetime, positioning this as a balanced middle ground between security benefits and operational practicality.
Apple proposed the more aggressive 47-day timeline that ultimately gained approval. Notably, Google quickly endorsed Apple’s proposal once voting commenced, signaling broad industry alignment despite initial disagreements. This unified support from major browser vendors effectively ensured passage, given their influential role in establishing web security standards.
Certificate authorities participated extensively in refining the proposal. Their feedback shaped transition timelines and validation reuse periods, balancing security objectives with practical implementation considerations. The final ballot reflects compromise and collaboration across competing interests, producing a workable framework for the entire ecosystem.
What the Mandate Actually Requires
The approved regulations establish three distinct types of requirements affecting certificate management. Understanding each component helps organizations plan comprehensive compliance strategies rather than addressing individual elements in isolation.
First, the maximum certificate lifetime itself decreases according to a phased schedule. Certificates issued after each implementation date cannot exceed the specified validity period. This applies universally to all publicly trusted TLS certificates, regardless of validation type or certificate authority.
Second, domain and IP address validation information has separate reuse limitations. Organizations cannot indefinitely reuse a single domain verification to issue multiple certificates. Instead, validation evidence expires according to the mandate’s schedule, requiring fresh verification after specified intervals.
Third, Subject Identity Information validation for Organization Validated and Extended Validation certificates follows its own timeline. The company name, address, and other organizational details included in these certificate types must be revalidated more frequently than previously required.
Certificate Lifetime Restrictions
Maximum validity periods for TLS certificates issued after each date:
- Until March 15, 2026: 398 days maximum
- March 15, 2026 onward: 200 days maximum
- March 15, 2027 onward: 100 days maximum
- March 15, 2029 onward: 47 days maximum
Domain Validation Reuse Limits
Maximum period for reusing domain ownership verification:
- Until March 15, 2026: 398 days reuse
- March 15, 2026 onward: 200 days reuse
- March 15, 2027 onward: 100 days reuse
- March 15, 2029 onward: 10 days reuse only
Critical Detail: The dramatically shortened validation reuse period of just 10 days beginning March 15, 2029, eliminates manual revalidation as a practical strategy. Organizations cannot realistically revalidate domain ownership every 10 days for certificate renewals occurring every 47 days. This design intentionally forces automation adoption.
Why 47 Days Specifically?
The number appears unusual at first glance, but follows deliberate logic. The formula accounts for the longest possible month plus half a standard month, with buffer time included. This calculation yields one maximum-length month of 31 days, plus a half-month of 15 days, plus one day of flexibility, totaling 47 days.
This mathematical approach ensures practical implementation windows. Organizations receive sufficient time to detect approaching expiration, execute renewal processes, and deploy updated certificates before current ones expire. The buffer prevents the aggressive timeline from creating unnecessary operational stress when automation handles the process correctly.
The same formula scaled differently produced the 200-day and 100-day intermediate steps. Each phase maintains consistent proportional relationships, providing predictable patterns as organizations adapt their systems progressively rather than facing a single dramatic change.
The Technical Timeline Breakdown
Three specific dates define the transition path from current practices to the final 47-day lifetime requirement. Each milestone introduces new constraints while allowing organizations time to adjust processes, implement automation, and validate readiness before the next phase begins.
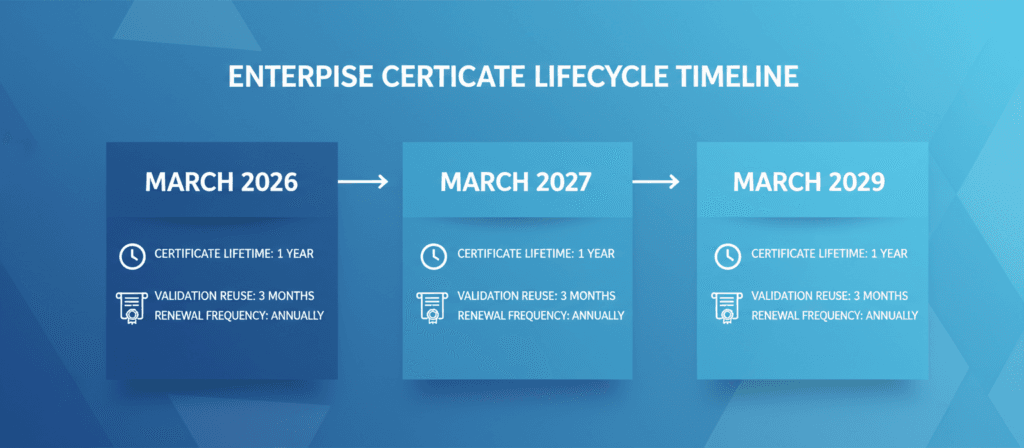
Phase One: March 15, 2026 Implementation
The initial reduction takes effect on March 15, 2026, when maximum certificate lifetime drops to 200 days. This represents the first mandatory change, cutting the current 398-day maximum nearly in half. Organizations will experience doubled renewal frequency compared to present practices.
Domain validation reuse periods also decrease to 200 days at this milestone. Certificate authorities can reuse domain ownership verification for 200 days after initial validation, meaning organizations that revalidate domains can potentially issue multiple certificates within that window without repeating verification steps each time.
Subject Identity Information validation for Organization Validated and Extended Validation certificates receives a separate limitation at this phase. Company details can be reused for 398 days, providing longer validity than domain verification. This recognizes that organizational information changes less frequently than domain configurations.
Certificate Parameters
- Maximum validity: 200 days
- Renewals per year: Approximately 2
- Reduction from current: 50% shorter
Validation Reuse Windows
- Domain validation: 200 days
- Organization validation: 398 days
- Manual processes: Still feasible
Operational Impact
- Moderate automation pressure
- Transition period begins
- Planning becomes critical
Phase Two: March 15, 2027 Implementation
The second reduction occurs exactly one year later on March 15, 2027. Maximum certificate lifetime falls to 100 days, requiring approximately four renewals annually. Manual management becomes significantly more burdensome at this stage, creating strong incentives for automation adoption.
Domain validation reuse periods similarly compress to 100 days. Organizations can still theoretically manage certificates manually at this phase, but the workload multiplies substantially. Companies with dozens or hundreds of certificates face continuous renewal cycles consuming considerable staff time.
This phase serves as the final practical window for implementing automation before the mandate makes manual processes entirely unworkable. Organizations delaying automation beyond this point risk serious operational disruptions when the third phase arrives.
Phase Three: March 15, 2029 Final Implementation
The ultimate milestone arrives on March 15, 2029, when maximum certificate lifetime reaches its final target of 47 days. Organizations will renew certificates more than seven times annually, making automation absolutely essential rather than merely beneficial.
Domain validation reuse periods collapse to just 10 days at this stage. This extreme limitation eliminates manual revalidation as a viable approach. Even organizations attempting to manually verify domain ownership every 10 days would find the process consuming and error-prone.
The design of this final phase intentionally leaves no practical alternative to automation. The CA/Browser Forum explicitly acknowledged this intent, stating the industry has been signaling for years that automation represents the only sustainable approach to certificate lifecycle management.
| Implementation Date | Certificate Lifetime | Domain Validation Reuse | Annual Renewals | Automation Status |
| Current through March 14, 2026 | 398 days | 398 days | ~1 per year | Optional |
| March 15, 2026 | 200 days | 200 days | ~2 per year | Recommended |
| March 15, 2027 | 100 days | 100 days | ~4 per year | Highly Recommended |
| March 15, 2029 | 47 days | 10 days | ~8 per year | Mandatory |
Planning Your Organization’s Timeline
Understanding these dates helps organizations construct realistic implementation schedules. Waiting until each deadline approaches guarantees rushed deployment, inadequate testing, and heightened risk of service disruptions from certificate expiration.
Best practices suggest beginning automation initiatives at least 12 months before the first deadline affecting your operations. For most organizations, this means starting preparation immediately or in early 2025 at the latest. The time requirement reflects not just technical implementation but also process redesign, team training, and gradual migration of existing certificates.
Organizations should target completing primary system automation before the March 2026 deadline, providing buffer time to address unexpected issues. Secondary systems can migrate by the March 2027 deadline, while the period until March 2029 serves as contingency for edge cases and legacy system remediation.
Why Manual Certificate Management Fails at Scale
Traditional certificate management relies heavily on manual processes. IT staff generate certificate signing requests, submit them to certificate authorities, complete domain validation procedures, download issued certificates, install them on web servers, and verify proper functionality. Each step requires human attention and execution.
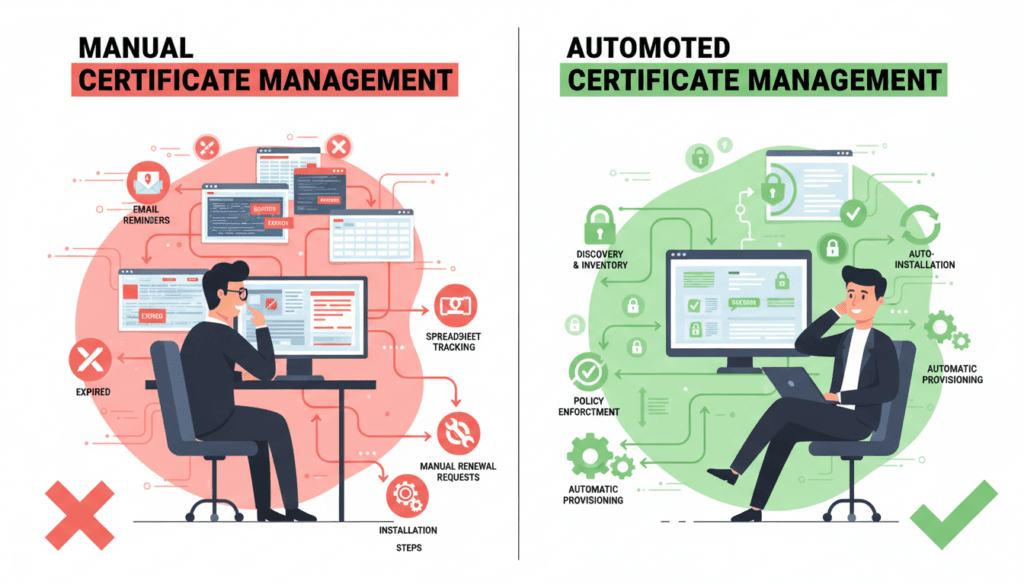
This approach functioned adequately when certificates remained valid for multiple years. Annual or semi-annual renewal cycles allowed teams to schedule maintenance windows, coordinate across departments, and allocate dedicated staff time. The relatively low frequency made manual handling sustainable despite inefficiency.
The Mathematics of Manual Certificate Management
Simple arithmetic reveals why manual processes cannot scale to 47-day lifetimes. Consider an organization managing 100 certificates across various domains and services. Under current 398-day lifetimes, this requires approximately 100 renewal operations annually, or roughly two per week.
At 47-day lifetimes, the same 100 certificates require nearly 800 renewal operations annually. This translates to more than 15 renewals weekly, or multiple renewals every single business day. Each renewal consumes time for generation, submission, validation, installation, and verification.
Even assuming highly efficient 15-minute renewals, this workload demands 200 hours annually just for certificate operations. That equals five full work weeks devoted exclusively to certificate management, excluding time for troubleshooting problems, coordinating with teams, or addressing expiration emergencies.
Workload Calculation Example
Organization with 100 certificates at 47-day lifetimes:
- Total annual renewals: 776 operations
- Weekly renewal frequency: 15 renewals
- Daily renewal frequency: 3 renewals
- Time per renewal: 15-30 minutes
- Annual labor hours: 200-400 hours
- Full-time equivalent: 0.1-0.2 FTE
This calculation excludes troubleshooting, emergency renewals, coordination overhead, and documentation requirements.

Human Error Multiplies With Frequency
Manual processes inherently carry error risk. Even experienced administrators occasionally misconfigure certificate installations, select incorrect validation methods, or overlook expiration notifications. When these events occur once or twice yearly, teams can absorb the impact without significant business disruption.
Multiplying operation frequency eight-fold dramatically increases error probability. An administrator maintaining 99% accuracy across 100 annual operations produces one error per year. That same accuracy rate across 800 annual operations generates eight errors yearly, transforming rare incidents into regular occurrences.
Certificate expiration causes particularly severe problems. When a TLS certificate expires on a production web server, browsers immediately display security warnings to visitors. Most users abandon the site rather than proceeding through warning screens, directly impacting revenue, reputation, and customer trust.
Coordination Complexity Grows Exponentially
Certificate operations rarely involve a single individual. Many organizations require coordination between security teams who manage certificate authorities, network teams who control load balancers, application teams who maintain web servers, and operations teams who schedule maintenance windows.
Each renewal cycle requires scheduling, communication, and validation across these groups. At annual frequency, teams can establish routine processes. At eight-times-annual frequency, certificate renewals become continuous operations consuming perpetual attention rather than occasional maintenance tasks.
Calendar scheduling alone becomes problematic. Organizations must identify eight suitable maintenance windows annually for each certificate, avoiding holidays, high-traffic periods, and conflicting project deadlines. Multiply this by 100 certificates and the coordination effort becomes substantial.
Real-World Incident: A major cloud provider experienced a significant outage in 2020 when a root certificate expired unexpectedly. The incident affected millions of devices globally, caused service disruptions lasting hours, and generated estimated losses exceeding $100 million. With 47-day certificate lifetimes, such incidents become statistically more likely without comprehensive automation.
Visibility and Tracking Challenges
Organizations struggle to maintain accurate inventories of deployed certificates even with current annual renewal cycles. Certificates get installed on development servers, test environments, internal applications, and forgotten infrastructure. These “shadow certificates” often escape centralized tracking until they expire and cause outages.
Manual tracking through spreadsheets or ticketing systems cannot reliably capture the complete certificate landscape in large organizations. Documentation falls out of date as staff deploy new services, decommission old systems, or make emergency changes. The faster certificates cycle, the more quickly this information becomes obsolete.
Lack of visibility creates compliance risks beyond operational concerns. Security audits, regulatory examinations, and certification processes often require organizations to demonstrate current certificate inventories and renewal evidence. Manual systems cannot provide this documentation reliably at scale.
Security Advantages of Shorter TLS Certificate Lifetimes
The CA/Browser Forum’s decision prioritizes security improvements over operational convenience. While shorter lifetimes create management challenges, they deliver substantial security benefits that strengthen the overall internet trust ecosystem. Understanding these advantages helps organizations appreciate the mandate’s strategic value beyond mere compliance.

Limiting Cryptographic Key Exposure Windows
Every TLS certificate contains a server public key paired with a corresponding private key stored securely on the server. When establishing secure connections, clients use the public key to encrypt session keys, which only the legitimate server possessing the private key can decrypt. This public-private key infrastructure forms the foundation of Transport Layer Security.
Private key compromise represents a critical security breach. Attackers obtaining a private key can impersonate the legitimate server, intercept encrypted communications, and potentially decrypt previously captured traffic if perfect forward secrecy wasn’t implemented. The longer a certificate remains valid, the longer a compromised private key retains utility for attackers.
Traditional long-lived certificates created extended risk windows. A private key compromised early in a certificate’s validity period could be exploited for an entire year or more before natural expiration. Even if organizations detected the breach, revocation mechanisms often failed to prevent continued exploitation.
Shorter certificate lifetimes dramatically compress these exposure windows. A private key compromised under a 47-day regime loses value within weeks rather than months or years. This reduction limits the damage attackers can inflict and decreases the return on investment for sophisticated key extraction efforts.
Forcing Cryptographic Agility Through Frequent Rotation
Security best practices have long recommended regular key rotation as a fundamental hygiene measure. Cryptographic keys, like passwords, should change periodically to limit exposure from undetected compromises. However, manual key rotation for certificates occurred rarely in practice due to operational complexity.
Automated 47-day renewal cycles inherently enforce key rotation discipline. Each renewal typically generates fresh key pairs rather than reusing existing ones. This practice ensures that even if a private key becomes compromised without detection, its useful lifetime to attackers remains strictly limited.
Frequent rotation also prepares organizations for future cryptographic transitions. When quantum computing threatens current encryption algorithms, the industry will need to migrate to post-quantum cryptography rapidly. Organizations already rotating certificates every 47 days can execute this transition within months rather than years.
Improving Certificate Information Accuracy
TLS certificates contain more than just cryptographic keys. Organization Validated and Extended Validation certificates include company names, addresses, and contact information. Even Domain Validated certificates associate specific domain names with certificate ownership at the time of issuance.
This information loses accuracy over time. Companies get acquired or restructured, domains change ownership, contact information becomes outdated, and organizational details shift. Long-lived certificates perpetuate obsolete information, potentially misleading users about current ownership and organizational status.
Frequent revalidation through short certificate lifetimes ensures this information remains current. When domains change hands, old certificates expire within weeks. When companies restructure, organizational details get refreshed during the next renewal cycle. This accuracy strengthens trust and reduces potential for confusion or deception.
Security Benefits of 47-Day Lifetimes
- Compromised private keys lose value within weeks
- Enforced cryptographic key rotation every renewal
- Certificate information remains current and accurate
- Reduced dependency on unreliable revocation systems
- Faster response capability to cryptographic vulnerabilities
- Shortened exposure windows for issuance errors
- Improved organizational security discipline
Implementation Challenges
- Requires investment in automation infrastructure
- Demands process redesign and documentation updates
- Necessitates staff training on new tools and workflows
- May require legacy system upgrades or replacements
- Increases monitoring and alerting requirements
- Creates temporary operational complexity during transition
Reducing Reliance on Broken Revocation Systems
Certificate revocation systems theoretically allow certificate authorities to invalidate compromised or incorrectly issued certificates before their natural expiration. Two primary mechanisms exist: Certificate Revocation Lists distributed periodically, and Online Certificate Status Protocol providing real-time checking.
In practice, both systems suffer from reliability problems. Many browsers don’t consistently check revocation status, either ignoring CRL downloads or failing gracefully when OCSP queries time out. This behavior prioritizes user experience over security, but undermines the revocation system’s effectiveness.
The CA/Browser Forum’s ballot explicitly acknowledges these revocation system failures. Short certificate lifetimes mitigate the impact by ensuring that even completely unrevoked compromised certificates expire quickly. A malicious actor exploiting a stolen certificate can only do so for 47 days maximum rather than a full year.
This approach accepts revocation system limitations as reality rather than hoping for future fixes. By designing security around the assumption that revocation won’t work reliably, the industry builds more robust protection into the certificate infrastructure itself.
Enabling Rapid Response to Vulnerabilities
Cryptographic vulnerabilities occasionally emerge in algorithms previously considered secure. The industry discovered critical weaknesses in SHA-1 hashing, certain RSA key sizes, and SSL protocol versions over the years. Migrating away from vulnerable cryptography requires replacing all affected certificates.
Long certificate lifetimes slow these transitions dramatically. Organizations cannot force clients to update certificates that won’t expire for months or years. The industry must wait for natural certificate turnover while known vulnerabilities remain exploitable.
Short lifetimes enable rapid cryptographic migrations. When vulnerabilities emerge, certificate authorities can update default parameters immediately. Within weeks or months, the entire ecosystem rotates to new, secure configurations through natural renewal cycles. This agility becomes increasingly important as cryptographic research advances and new threats emerge.
Real-World Impact on Enterprise Operations
The certificate lifetime reduction affects organizations across every industry and geographic region. Understanding specific operational impacts helps companies prepare comprehensive response strategies rather than treating this as purely a technical infrastructure change.
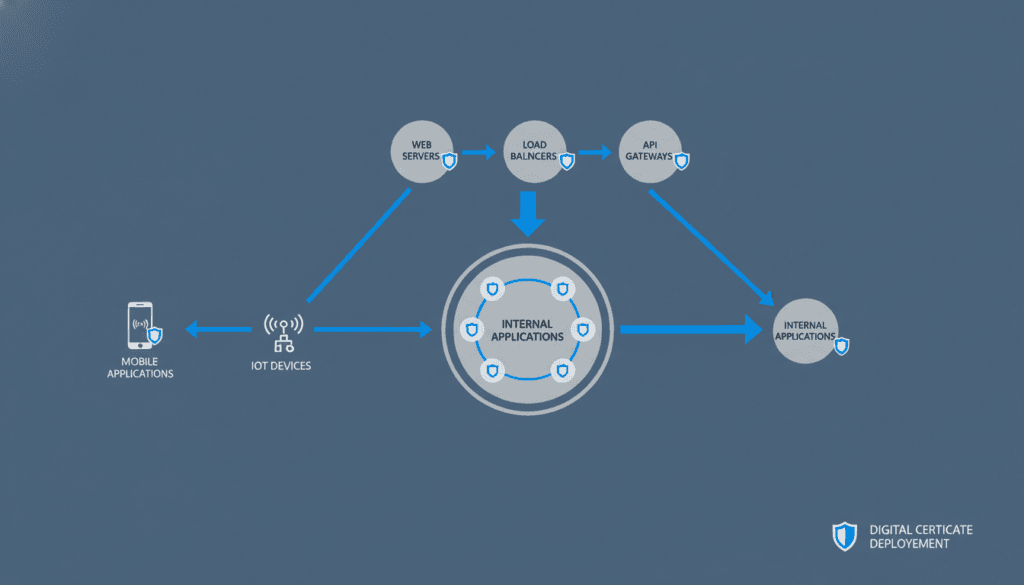
Public-Facing Web Properties
Customer-facing websites represent the most visible certificate deployment point. These sites require valid TLS certificates to display the browser padlock icon and avoid security warnings. Certificate expiration on primary web properties immediately impacts customer experience, often driving visitors away before they can complete purchases or access services.
E-commerce sites face particularly acute risks. Studies consistently show that browser security warnings cause abandoned shopping carts and lost revenue. During peak shopping periods like holiday seasons, certificate expiration could cost thousands or millions in lost sales within hours.
Content delivery networks add complexity to public website certificate management. Organizations distributing content across multiple geographic edge locations must coordinate certificate deployment to every CDN node. Manual processes struggle to maintain consistency across distributed infrastructure.
Internal Applications and Services
Enterprise applications used by employees often rely on TLS certificates despite their internal nature. HR systems, collaboration platforms, business intelligence tools, and document management systems all implement transport layer security to protect sensitive employee and company data.
Internal certificate expiration disrupts employee productivity. When certificates expire on critical business applications, staff cannot access systems needed for daily work. IT teams face pressure to restore access immediately, often rushing certificate renewal without proper testing or documentation.
The internal application landscape typically includes more certificates than public-facing properties. Organizations deploy separate certificates for each application, environment tier, and functional component. This proliferation multiplies management overhead under short lifetime requirements.
API Endpoints and Microservices
Modern application architectures rely heavily on APIs for communication between services. Mobile apps call backend APIs, third-party integrations access organizational data through API endpoints, and microservices communicate using REST or gRPC protocols. Each connection requires TLS certificates for secure communication.
API certificate management presents unique challenges. APIs often lack user interfaces for manual certificate installation. Instead, certificates must be deployed through automation, configuration management systems, or orchestration platforms. Organizations without existing automation infrastructure struggle to manage API certificates effectively.
Microservices architectures multiply these challenges exponentially. A single application might decompose into dozens of independent services, each requiring its own certificate. Service mesh technologies help manage this complexity but require careful implementation and ongoing maintenance.
Web Server Certificates
- Customer-facing websites
- E-commerce platforms
- Marketing sites and blogs
- Customer portals
- Content delivery networks
Application Certificates
- Internal business applications
- SaaS platform interfaces
- Database connection encryption
- Email server protection
- VPN gateway authentication
Infrastructure Certificates
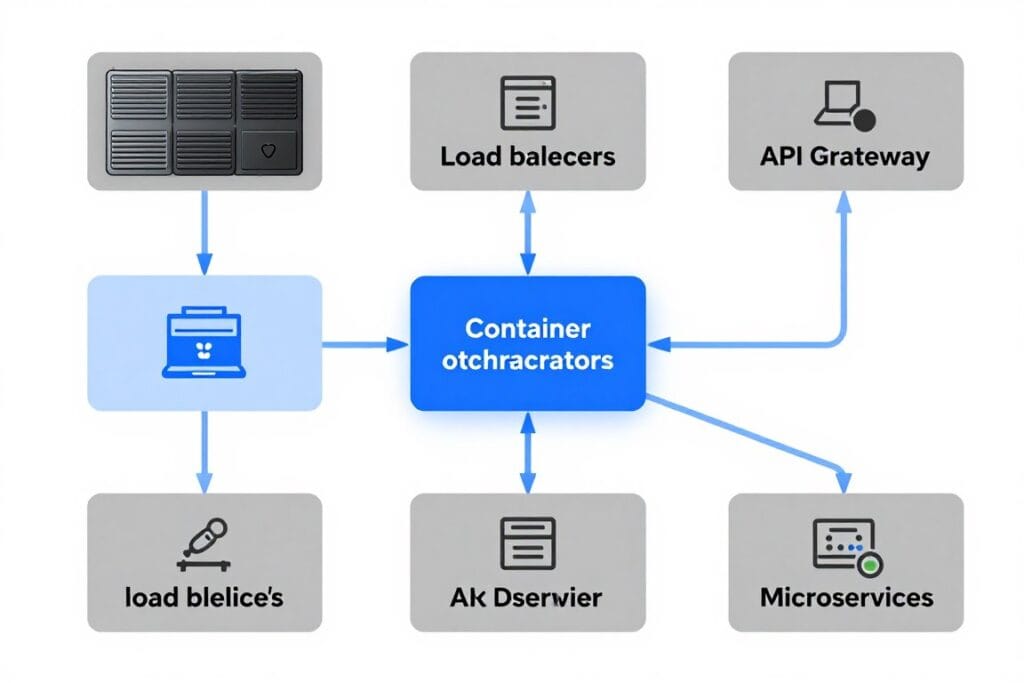
- Load balancers and reverse proxies
- API gateways
- Microservices communication
- Container orchestration
- IoT device authentication
Mobile Application Backend Security
Mobile apps communicate with backend servers through encrypted channels secured by TLS certificates. Unlike web browsers that users can easily update, mobile apps get distributed through app stores with specific server certificate expectations embedded in the application code.
Certificate pinning, a security technique where apps validate specific certificate properties, becomes problematic with short lifetimes. Apps using hard-coded certificate fingerprints will break when certificates renew. Organizations must either abandon certificate pinning or implement dynamic pinning approaches that work with automated certificate rotation.
Push notification services, in-app payment processing, and real-time messaging all depend on secure server connections. Certificate expiration can break these features silently, creating degraded user experiences that may not generate obvious error messages but definitely impact customer satisfaction.
IoT Device Certification
Internet of Things devices increasingly require TLS certificates for authentication and communication. Industrial sensors, building management systems, connected vehicles, and smart home devices all use certificates to establish secure connections with control servers.
IoT presents unique certificate management challenges. Devices often have limited computational resources, restricted network connectivity, and minimal user interfaces. Updating certificates on distributed IoT fleets requires over-the-air update mechanisms that many legacy device designs lack.
Device lifecycles compound these problems. IoT devices may remain deployed for years or decades with minimal maintenance. Designing for 47-day certificate lifetimes requires fundamentally rethinking device security architecture to support automated certificate renewal throughout the entire operational lifetime.
Assess Your Certificate Infrastructure Readiness
Understanding how the 47-day mandate affects your specific environment is the first step toward successful compliance. Our certificate management experts can evaluate your current infrastructure, identify automation opportunities, and design a transition roadmap tailored to your organization’s needs and timeline.
ACME Protocol and Automation Standards
The Automated Certificate Management Environment protocol has emerged as the industry standard for certificate automation. ACME provides a standardized method for web servers to prove domain ownership, request certificate issuance, and automate renewal processes without human intervention. Understanding ACME capabilities and limitations helps organizations select appropriate automation approaches.
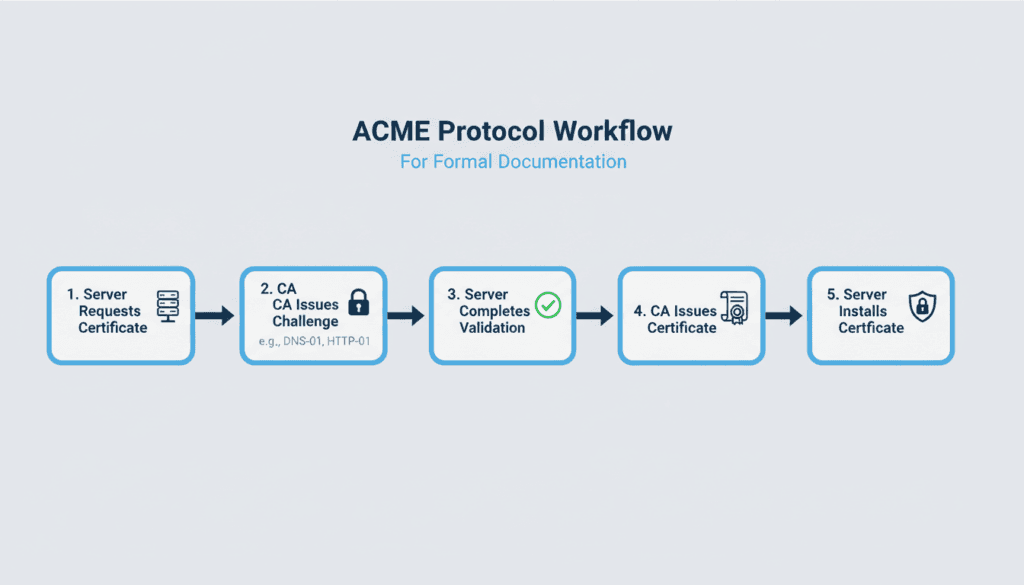
How ACME Protocol Works
ACME operates through a challenge-response mechanism that proves domain control without manual intervention. When a server requests a certificate, the certificate authority issues a challenge that only the legitimate domain controller can complete. Common challenge types include placing specific files at designated web locations or creating particular DNS records.
The server’s ACME client automatically receives the challenge, completes the required action, and notifies the certificate authority to verify completion. Upon successful validation, the CA immediately issues the requested certificate. The entire process typically completes within minutes, enabling truly automated certificate lifecycle management.
ACME clients handle the complete certificate lifecycle. They automatically generate key pairs, create certificate signing requests, complete domain validation challenges, retrieve issued certificates, install certificates on web servers, and track expiration dates for proactive renewal. Organizations configure the client once and it operates autonomously thereafter.
ACME Renewal Information Extension
ACME Renewal Information represents an important protocol extension that optimizes renewal timing. Traditional renewal approaches used fixed time windows before expiration, renewing certificates when they reached a certain age. This created predictable but inflexible renewal schedules that didn’t account for certificate authority operational considerations.
ARI allows certificate authorities to communicate optimal renewal windows for each specific certificate. CAs can recommend renewing certain certificates earlier due to planned maintenance, security concerns, or operational needs. Clients respecting ARI recommendations distribute renewal load more evenly and avoid potential availability issues.
Under 47-day lifetimes, renewal timing becomes increasingly important. Renewing too early wastes valid certificate days, while renewing too late risks expiration if problems occur. ARI balances these concerns by providing CA-specific guidance that optimizes both security and operational efficiency.
Validation Methods for Different Certificate Types
ACME initially targeted Domain Validated certificates, the simplest validation type that only confirms domain control. Modern ACME implementations now support Organization Validated and Extended Validation certificates that require additional identity verification beyond domain ownership.
Organization Validated certificate automation leverages pre-validated organization information. After completing initial manual organization validation, ACME clients can automatically issue OV certificates using that validated information for the allowed reuse period. This semi-automated approach reduces workload while maintaining required identity verification.
Extended Validation certificates require more extensive identity verification, including legal existence confirmation and operational presence validation. While complete EV automation remains limited, modern systems automate many components, reserving manual verification only for the most sensitive identity elements.
ACME Challenge Types
- HTTP-01: Places verification file at specific web server location
- DNS-01: Creates special DNS TXT record for domain
- TLS-ALPN-01: Uses TLS protocol extension for validation
- HTTP-01 for wildcard: Not supported, requires DNS-01
Each challenge type suits different environments and infrastructure configurations. DNS-01 proves particularly useful for wildcard certificates and internal systems without public HTTP access.
ACME Client Implementations
- Certbot: Official client with broad platform support
- Caddy: Web server with built-in ACME automation
- Traefik: Reverse proxy with native ACME integration
- acme.sh: Lightweight shell script implementation
- win-acme: Windows-focused ACME client
Choosing appropriate ACME clients depends on infrastructure, technical expertise, and integration requirements.
ACME Integration With Existing Infrastructure
Successful ACME implementation requires integration with existing IT infrastructure. Web servers need configuration updates to work with ACME clients. Load balancers require mechanisms to distribute certificates across multiple backend servers. DNS systems must support automated record creation for DNS-01 challenges.
Cloud platforms increasingly provide native ACME support. Major cloud providers offer integrated certificate management services that handle ACME protocols, DNS challenge completion, and certificate deployment to relevant services. These managed services reduce implementation complexity for cloud-native organizations.
Container orchestration platforms like Kubernetes benefit from specialized ACME integrations. Projects like cert-manager automate certificate provisioning for ingress controllers, handling the complete lifecycle from issuance through renewal and deployment. These tools abstract away ACME complexity, providing Kubernetes-native certificate management.
ACME Limitations and Alternative Approaches
While ACME provides excellent automation for many use cases, certain scenarios require alternative approaches. Systems without internet connectivity cannot complete ACME challenges that require certificate authority communication. Legacy applications may lack the ability to integrate with ACME clients effectively.
Certificate management platforms offer more comprehensive capabilities than standalone ACME clients. These platforms provide centralized visibility across all certificates, policy enforcement, compliance reporting, and integrations with multiple certificate authorities. They typically include ACME support alongside additional automation mechanisms.
Organizations managing diverse environments benefit from platforms that combine ACME automation with other certificate issuance methods. This hybrid approach allows standardization on a single management interface while supporting the full range of certificate use cases across the organization.
Building an Automated Certificate Infrastructure
Implementing comprehensive certificate automation requires more than deploying ACME clients. Organizations need strategic planning, architectural decisions, and phased implementation approaches that minimize risk while building toward fully automated certificate lifecycle management.
Certificate Discovery and Inventory
Automation begins with comprehensive visibility into existing certificate deployments. Many organizations lack accurate inventories of where certificates are deployed, which certificate authorities issued them, when they expire, and who owns responsibility for renewal.
Certificate discovery tools scan networks to identify all deployed certificates. These tools connect to servers, check certificate properties, and build centralized databases of certificate information. Discovery should run continuously, detecting new certificates as they’re deployed and removing entries when certificates are retired.
Accurate inventory enables risk assessment. Organizations can identify certificates approaching expiration, find certificates using weak cryptographic parameters, locate certificates from unexpected certificate authorities, and detect certificates deployed without proper authorization.
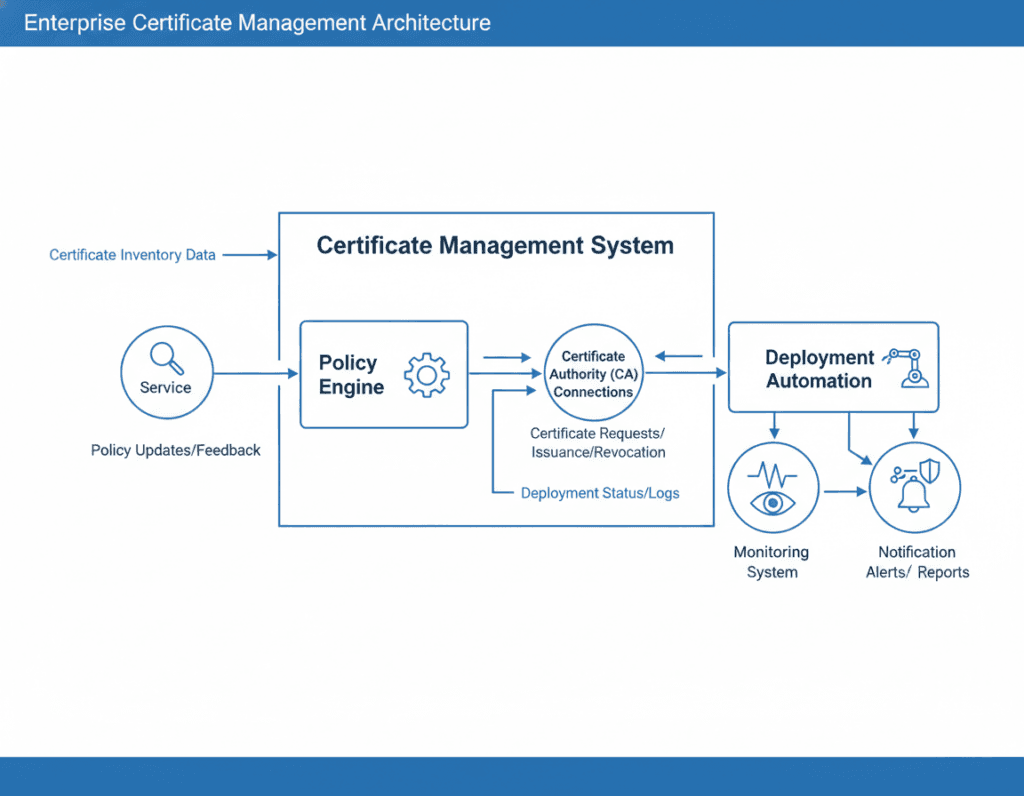
Centralized Certificate Management Platform
Certificate management platforms provide unified interfaces for controlling certificates across the organization. Rather than managing individual ACME clients on dozens or hundreds of servers, administrators configure policies centrally and the platform handles implementation details.
These platforms typically offer certificate request workflows, automated issuance through multiple certificate authorities, policy-based validation and approval, automated deployment to target systems, renewal tracking and automation, and comprehensive reporting and auditing capabilities.
Integration capabilities determine platform value. The best platforms connect with existing infrastructure including web servers, load balancers, API gateways, cloud platforms, container orchestrators, and monitoring systems. Native integrations reduce custom development requirements and accelerate implementation.
Core Platform Capabilities
- Automated certificate discovery across infrastructure
- Centralized certificate inventory and tracking
- Multi-CA support with unified interface
- Policy-based certificate issuance controls
- Automated validation and approval workflows
- Scheduled and event-driven renewal automation
- Automated certificate deployment
- Comprehensive audit logging and reporting
- Expiration alerting and notification
- Role-based access control and delegation
Policy-Based Certificate Governance
Automation should enforce organizational policies rather than simply executing certificate operations faster. Certificate policies define acceptable validation types, allowed certificate authorities, maximum validity periods, required cryptographic parameters, and approval requirements for different certificate types.
Policy engines evaluate certificate requests against defined rules before issuance. Requests violating policies get rejected automatically or routed for manual review. This prevents security policy violations while maintaining automation efficiency for compliant requests.
Different organizational units often require different certificate policies. Development environments might allow more permissive policies than production systems. Public-facing services might mandate specific certificate authorities while internal applications accept broader choices. Hierarchical policy structures accommodate these variations.
Deployment Automation and Orchestration
Issuing certificates solves only half the automation challenge. Organizations must also automate certificate deployment to target systems. Deployment automation transfers certificates to web servers, updates load balancer configurations, restarts services when necessary, and verifies successful deployment.
Deployment mechanisms vary by target system type. Web servers might use SSH-based file transfer and service restart commands. Load balancers often provide APIs for configuration updates. Cloud platforms offer native certificate management services. Container orchestrators use secrets management systems for certificate distribution.
Orchestration coordinates deployment across multiple systems simultaneously. When updating certificates for load-balanced services, orchestration ensures all backend servers receive updated certificates before removing old ones. This prevents intermittent connection failures during certificate rotation.
Monitoring, Alerting, and Incident Response
Comprehensive monitoring validates that automation works correctly. Monitoring systems should track certificate issuance success rates, validation failure reasons, deployment completion status, certificate expiration dates, and certificate usage patterns across infrastructure.
Alerting provides early warning of automation problems. Rather than discovering issues when certificates expire, organizations should receive alerts when renewal attempts fail, when certificates approach expiration without renewal scheduling, or when certificate deployments don’t complete successfully.
Incident response procedures define actions when automation fails. Clear escalation paths, documented troubleshooting procedures, and designated responsible teams ensure rapid problem resolution. Even with excellent automation, occasional failures will occur and require human intervention.
Phased Implementation Strategy
Organizations should implement certificate automation incrementally rather than attempting complete transformation simultaneously. Phased approaches reduce risk, allow learning from early deployments, and demonstrate value before demanding extensive resources.
Phase one typically focuses on certificate discovery and inventory. Understanding the current state provides the foundation for automation planning. This phase requires relatively low risk since it doesn’t modify production systems.
Phase two implements automation for non-critical systems. Development environments, test systems, and internal applications provide lower-risk automation targets. Teams can refine processes and resolve issues before tackling production systems.
Phase three extends automation to production systems incrementally. Start with redundant systems where certificate problems won’t cause complete outages. Gradually expand to more critical systems as confidence grows. Reserve the most sensitive systems for final implementation after proving automation reliability elsewhere.
Cost Analysis: Manual vs Automated Management
Organizations frequently question whether certificate automation justifies the required investment. Comprehensive cost analysis reveals that automation typically provides substantial return on investment, particularly under short certificate lifetime requirements. Understanding both direct and indirect costs helps build compelling business cases for automation initiatives.
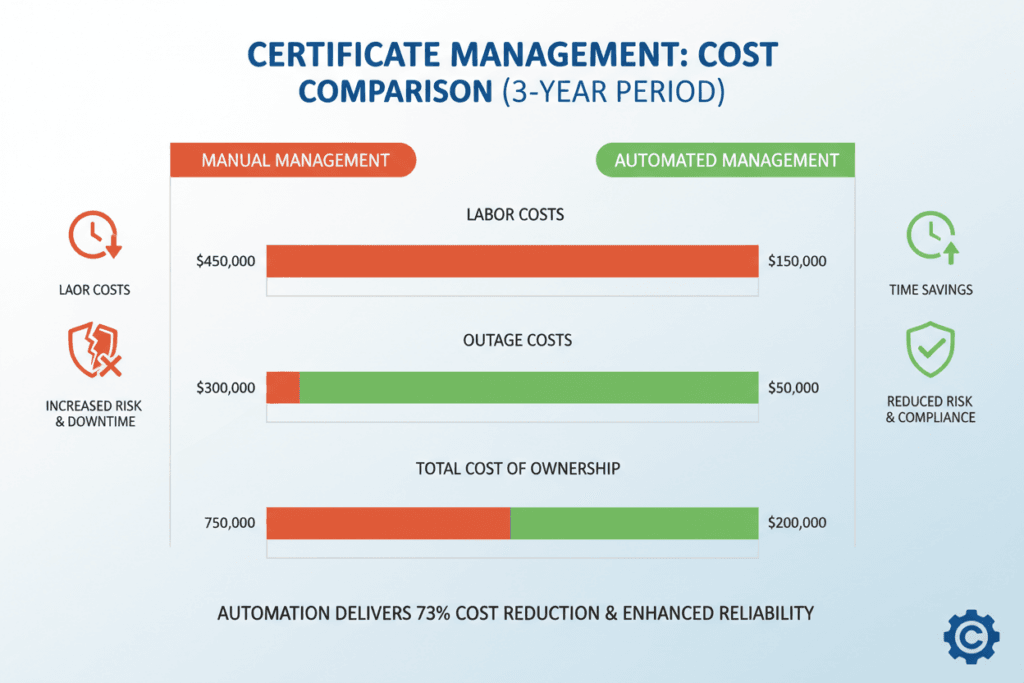
Direct Labor Cost Calculations
Labor represents the most obvious cost component in certificate management. Manual processes consume staff time for request generation, validation completion, certificate installation, testing, and documentation. Multiplying per-certificate labor hours by annual renewal frequency and loaded labor rates yields direct labor costs.
Consider an organization managing 500 certificates. Under current 398-day lifetimes requiring annual renewal, this represents 500 certificate operations yearly. Assuming 30 minutes per operation and $75 per hour loaded labor cost, annual direct labor costs equal $18,750.
At 47-day lifetimes, the same 500 certificates require approximately 3,900 operations annually. Using identical per-operation assumptions, annual direct labor costs increase to $146,250. This $127,500 annual increase far exceeds typical certificate automation platform costs, creating clear economic justification for automation investment.
| Certificate Count | Annual Renewals (398-day) | Annual Renewals (47-day) | Labor Cost (398-day) | Labor Cost (47-day) | Annual Increase |
| 100 certificates | 100 operations | 776 operations | $3,750 | $29,100 | $25,350 |
| 500 certificates | 500 operations | 3,880 operations | $18,750 | $145,500 | $126,750 |
| 1,000 certificates | 1,000 operations | 7,766 operations | $37,500 | $291,000 | $253,500 |
| 5,000 certificates | 5,000 operations | 38,830 operations | $187,500 | $1,456,125 | $1,268,625 |
Assumptions: 30 minutes per renewal operation, $75/hour loaded labor rate. Actual costs vary by organization size, geography, and process efficiency.
Certificate Outage Cost Impact
Certificate expiration causes service outages with substantial business impact. E-commerce sites lose revenue directly when customers cannot complete purchases. B2B services breach service level agreements, triggering financial penalties. All organizations suffer reputation damage and customer trust erosion.
Outage costs vary dramatically by organization and service criticality. Small businesses might lose thousands per hour, while large enterprises could lose millions. Industry studies estimate average costs between $5,000 and $10,000 per hour for small to mid-size organizations, escalating to $100,000 or more hourly for large enterprises.
Manual certificate management increases outage probability significantly. Even assuming 99% renewal success rates, organizations managing 500 certificates at 47-day lifetimes experience approximately 39 failures annually. If even 10% of failures cause two-hour outages before resolution, that represents 8 outage hours yearly with costs ranging from $40,000 to $800,000 depending on organization size.
Hidden Costs of Manual Processes
Labor and outage costs represent direct, measurable impacts. Numerous hidden costs also affect total cost of ownership. Opportunity costs reflect how technical staff could contribute to strategic initiatives if freed from repetitive certificate management. Context switching costs accumulate when staff interrupt other work to handle certificate renewals.
Coordination overhead consumes significant time across multiple teams. Security teams, operations teams, development teams, and management all spend time on certificate-related communication, scheduling, and approvals. While individual interactions seem minor, cumulative coordination time across hundreds of annual certificate operations becomes substantial.
Compliance and audit costs increase with manual processes. Demonstrating certificate management compliance requires documentation, evidence collection, and audit support. Manual processes generate incomplete records, requiring additional effort to reconstruct certificate histories during audits. Automated systems provide comprehensive audit trails automatically, reducing compliance labor requirements.
Automation Investment Requirements
Certificate automation requires upfront investment in platforms, implementation services, and training. Enterprise certificate management platforms typically cost between $20,000 and $100,000 annually depending on certificate volumes and feature requirements. Implementation services might add $25,000 to $75,000 in initial costs.
Staff training represents additional investment. While modern platforms emphasize usability, teams need time to learn new tools and processes. Budget several thousand dollars per team member for training, plus productivity impacts during the learning curve.
Ongoing operational costs include platform subscription renewals, certificate authority fees, and staff time for system administration. However, these costs remain relatively stable as certificate volumes grow, unlike manual labor costs that scale linearly with certificate count.
ROI Example: An organization managing 500 certificates investing $75,000 in automation implementation plus $40,000 annual platform costs realizes $126,750 in annual labor savings at 47-day lifetimes. The investment pays for itself within the first year, with ongoing annual savings exceeding $86,000. Organizations managing more certificates achieve even faster ROI.
Risk Reduction Value
Beyond measurable costs, automation provides risk reduction value that’s difficult to quantify precisely but strategically significant. Reduced outage probability protects revenue and reputation. Improved security posture from frequent key rotation and current certificate information may reduce cyber insurance premiums or prevent breaches with massive remediation costs.
Compliance assurance prevents regulatory penalties and certification failures. Many industries face substantial fines for security control failures. Automated certificate management with comprehensive audit logging demonstrates control effectiveness, reducing compliance risk.
Competitive advantage emerges from freeing technical talent for innovation rather than maintenance. Organizations that automate repetitive tasks redirect staff toward revenue-generating projects, new feature development, and strategic initiatives. While difficult to assign precise dollar values, these strategic benefits often exceed direct cost savings.
Integration With Existing IT Systems
Certificate automation cannot operate in isolation. Successful implementation requires integration with the diverse systems and platforms that comprise modern IT infrastructure. Understanding integration requirements and approaches for different system types enables comprehensive automation coverage.
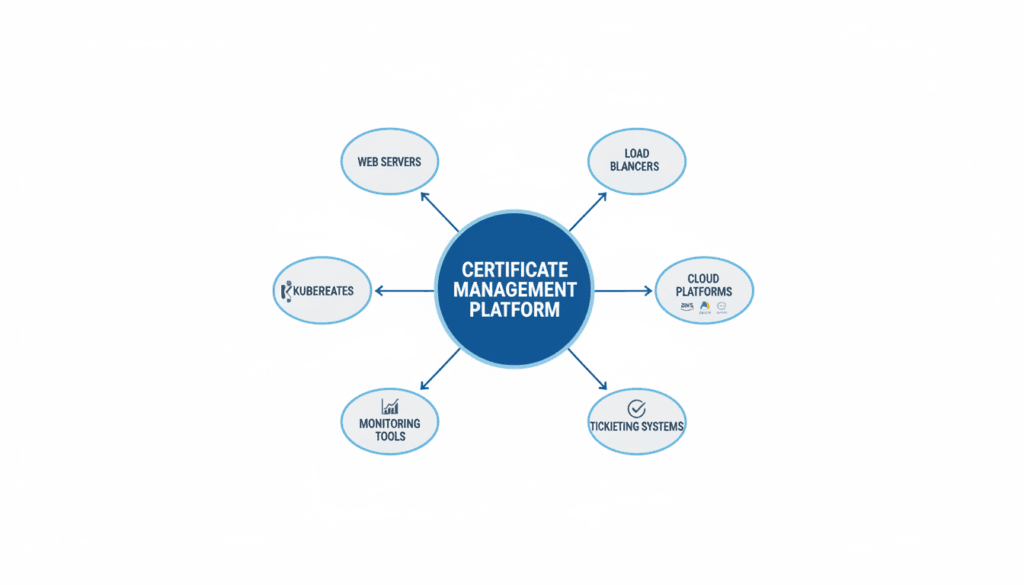
Web Server Integration
Web servers represent the most common certificate deployment target. Apache, Nginx, IIS, and other web server platforms each have unique certificate installation requirements. Automation must accommodate these differences while providing consistent management interfaces.
File-based certificate deployment works for many web servers. Automation systems transfer certificate files and private keys to specified server locations via SSH, SFTP, or other secure protocols. Configuration file updates point the web server to new certificate locations. Service restart commands activate the updated configuration.
API-based integration provides more sophisticated capabilities for web servers supporting programmatic configuration. Systems can query current certificate status, push configuration updates without manual file transfers, and verify successful deployment through API responses. This approach reduces error potential compared to file-based methods.
Load Balancer and Reverse Proxy Integration
Load balancers and reverse proxies often terminate TLS connections before forwarding requests to backend servers. This architecture centralizes certificate management at the load balancer layer, reducing the number of systems requiring certificates while creating critical single points of failure if certificate automation fails.
Major load balancer vendors provide APIs for certificate management. F5, Citrix NetScaler, HAProxy, and cloud-native load balancers expose endpoints for uploading certificates, binding them to virtual servers, and verifying configuration. Automation platforms integrate with these APIs to manage load balancer certificates programmatically.
High-availability load balancer configurations require synchronized certificate deployment across multiple units. Automation must coordinate certificate updates to all cluster members, ensuring consistent configuration. Rolling update strategies can minimize service disruption by updating standby units before active ones.
Cloud Platform Native Integration
Major cloud platforms provide native certificate management services that simplify automation for cloud-deployed applications. AWS Certificate Manager, Azure Key Vault, Google Cloud Certificate Manager, and similar services handle certificate issuance, renewal, and deployment to compatible cloud services automatically.
Integrating with cloud-native certificate services leverages platform capabilities while maintaining centralized oversight. Certificate management platforms can delegate actual issuance and renewal to cloud services while maintaining inventory, policy enforcement, and reporting centrally. This hybrid approach optimizes both platform-specific capabilities and enterprise-wide visibility.
Multi-cloud environments complicate integration requirements. Organizations using multiple cloud providers need certificate management solutions that integrate with all relevant platforms. Unified interfaces across AWS, Azure, and GCP reduce operational complexity and training requirements.
On-Premises Integration Patterns
- SSH/SFTP file transfer: Direct certificate file deployment to servers
- Configuration management: Integration with Ansible, Puppet, Chef
- API integration: Direct API calls to application management interfaces
- Agent-based: Lightweight agents on target systems handling deployment
- Service mesh: Integration with Istio, Linkerd for microservices
Cloud Integration Patterns
- AWS Certificate Manager: Native AWS service integration
- Azure Key Vault: Certificate storage and Azure service deployment
- GCP Certificate Manager: Google Cloud native certificate handling
- Cloud APIs: Platform-specific APIs for compute resources
- Kubernetes operators: Custom resource definitions for cloud K8s
Container Orchestration Integration
Kubernetes and other container orchestration platforms present unique certificate management challenges. Containers are ephemeral by design, making static certificate deployment impractical. Instead, certificates must be delivered dynamically as containers start and updated automatically throughout the container lifecycle.
Kubernetes Secrets provide native certificate storage and delivery mechanisms. Certificate management systems can create and update Secrets containing certificates and private keys. Applications reference these Secrets through volume mounts or environment variables, automatically receiving updated certificates when Secrets change.
Cert-manager and similar Kubernetes-native tools provide sophisticated certificate automation. These systems watch for certificate requests expressed as Kubernetes Custom Resources, automatically provision certificates through ACME or other protocols, store results in Secrets, and handle ongoing renewal. Integration with these tools extends enterprise certificate management into containerized environments.
Monitoring and Observability Integration
Certificate management systems should integrate with existing monitoring and observability platforms. Pushing certificate metrics, expiration dates, and renewal events to monitoring systems enables unified operational visibility. Teams can incorporate certificate health into overall system monitoring rather than checking separate certificate management interfaces.
Prometheus, Datadog, Splunk, and similar platforms can ingest certificate management metrics. Integration typically uses platform-specific APIs or agents. Key metrics include certificates approaching expiration, recent renewal successes and failures, validation error rates, and deployment success rates.
Alerting integration ensures appropriate teams receive notifications about certificate issues. Certificate expiration warnings should route to on-call staff through PagerDuty, Opsgenie, or similar systems. Alert routing can escalate based on certificate criticality, providing proportional response to different severity levels.
IT Service Management Integration
Certificate operations often require coordination with change management, incident management, and approval workflows. Integration with IT service management platforms like ServiceNow, Jira Service Management, or BMC Remedy streamlines these processes.
Automated change request creation documents certificate renewals for audit purposes. When automation systems deploy certificates, they can automatically generate change records including deployment details, affected systems, and timestamps. This satisfies change management requirements without manual paperwork.
Incident management integration helps coordinate certificate-related problems. When certificate automation failures occur, systems can automatically create incident tickets with relevant diagnostic information. This accelerates problem resolution by immediately engaging appropriate teams with necessary context.
Expert Implementation Services
Integrating certificate automation with your unique IT environment requires deep expertise in both certificate management and your specific technology stack. Our implementation specialists bring proven experience across diverse environments, from legacy infrastructure to cloud-native architectures. Let us design and implement an automation solution tailored to your systems and requirements.
Certificate Authority Perspectives and Support
Certificate authorities play critical roles in the transition to shorter certificate lifetimes. Their technical capabilities, automation support, and customer assistance programs directly impact how smoothly organizations can adapt to the new requirements. Understanding CA perspectives and offerings helps organizations select appropriate partners for their automation journey.
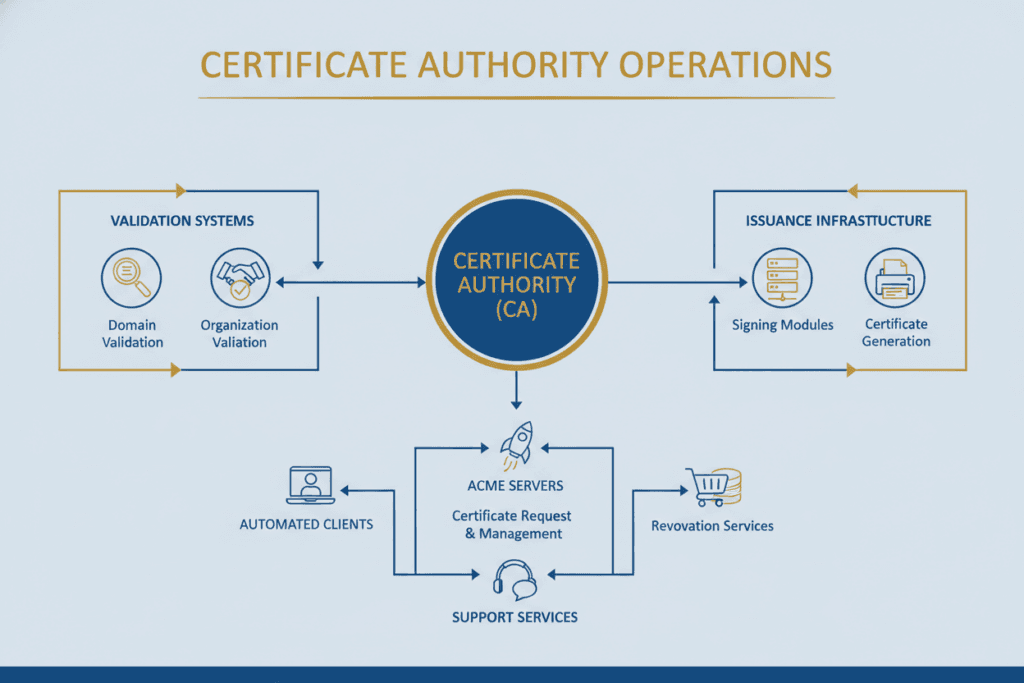
Industry-Wide CA Support for the Mandate
Major certificate authorities have expressed support for shorter certificate lifetimes despite the operational complexity involved. CAs recognize that frequent renewals require robust automation infrastructure on both provider and customer sides. Leading CAs have invested significantly in ACME protocol support, API capabilities, and customer education programs.
DigiCert has been particularly vocal about supporting customers through the transition. Their blog post announcing the ballot results emphasized that automation is now non-negotiable rather than optional. DigiCert offers Trust Lifecycle Manager and CertCentral platforms with comprehensive automation capabilities including ACME support for DV, OV, and EV certificates.
Sectigo, Let’s Encrypt, GlobalSign, and other major CAs have similarly enhanced their automation capabilities. The competitive marketplace incentivizes CAs to provide superior automation tools and customer support, benefiting organizations navigating the transition.
ACME Implementation Maturity Across CAs
Not all certificate authorities offer identical ACME capabilities. Let’s Encrypt pioneered ACME adoption and provides comprehensive free certificate issuance for Domain Validated certificates. Their infrastructure handles millions of automated certificate issuances daily, demonstrating ACME’s scalability.
Commercial CAs have progressively enhanced ACME support beyond basic Domain Validated certificates. Modern implementations support Organization Validated certificates through ACME by separating domain validation from organization validation. The domain validation occurs automatically via ACME, while organization information uses pre-validated data from initial manual verification.
Extended Validation certificate automation remains more limited. EV requirements include telephone verification, legal documentation review, and operational existence confirmation. While CAs are developing semi-automated EV workflows, fully automated EV issuance without human involvement hasn’t achieved widespread adoption.
Certificate Authority Pricing Models
A common concern about shorter certificate lifetimes involves potential cost increases. Organizations worry that eight renewals annually instead of one might increase certificate costs proportionally. Certificate authorities have addressed this concern through subscription-based pricing models.
Most commercial CAs charge based on annual subscriptions covering unlimited reissuances within the subscription period. Whether an organization renews certificates twice or eight times during the year, the cost remains constant. This pricing model removes economic barriers to automation and frequent renewal.
Volume-based pricing provides additional economies of scale for large certificate portfolios. Organizations managing hundreds or thousands of certificates typically negotiate volume discounts that significantly reduce per-certificate costs compared to small-volume purchases.
CA Technical Capabilities
- Full ACME protocol support including ARI
- RESTful APIs for programmatic certificate management
- Bulk certificate operations and batch processing
- Webhook notifications for certificate events
- Multi-factor authentication for administrative access
- IP address allowlisting for API security
CA Automation Support
- Comprehensive API documentation and examples
- Client libraries in multiple programming languages
- Integration guides for common platforms
- Sandbox environments for testing
- Technical support for implementation assistance
- Regular webinars and training programs
CA Customer Services
- Dedicated account management teams
- Migration assistance from other CAs
- Custom integration development services
- Certificate inventory and discovery tools
- Compliance reporting and audit support
- 24/7 technical support availability
CA Migration and Multi-CA Strategies
Organizations sometimes need to change certificate authorities to access better automation capabilities or more favorable pricing. CA migration introduces complexity, requiring certificate reissuance across potentially thousands of systems.
Certificate authorities typically provide migration assistance programs for new customers. These services include certificate inventory tools to identify all existing certificates, bulk migration utilities to streamline reissuance, technical support throughout the migration process, and sometimes professional services for complex migrations.
Multi-CA strategies provide redundancy and flexibility. Rather than relying on a single certificate authority, organizations can maintain relationships with multiple CAs. Certificate management platforms can integrate with multiple CAs simultaneously, allowing policy-based selection of which CA issues each certificate.
CA-Provided Certificate Management Platforms
Many certificate authorities offer their own certificate management platforms in addition to raw certificate issuance capabilities. These platforms provide discovery tools, centralized management interfaces, automated renewal, deployment capabilities, and reporting functions specifically designed to work with that CA’s services.
CA-provided platforms offer tight integration with the provider’s issuance infrastructure. They understand CA-specific capabilities, optimize for that CA’s validation requirements, and provide streamlined workflows. However, organizations using multiple CAs may prefer independent certificate management platforms that work equally well with all CAs.
Platform selection depends on organizational requirements. Companies exclusively using one CA might prefer that CA’s platform for optimized integration. Organizations with multi-CA strategies or those anticipating future CA changes benefit from CA-agnostic platforms that provide consistent management regardless of underlying certificate provider.
Preparing Your Organization for the Transition
Successfully navigating the shift to 47-day certificate lifetimes requires comprehensive organizational preparation extending beyond technical implementation. Strategic planning, stakeholder alignment, resource allocation, and change management all contribute to smooth transitions with minimal business disruption.
Executive Sponsorship and Business Case Development
Certificate automation initiatives require executive sponsorship to succeed. Technical teams need authority to make architectural decisions, budget allocation for platform purchases and implementation services, and organizational priority to dedicate staff time. Building compelling business cases helps secure necessary executive support.
Effective business cases emphasize risk reduction alongside cost savings. While labor cost reductions provide quantifiable benefits, risk mitigation often resonates more strongly with executives. Highlight revenue protection from outage prevention, reputation preservation through reliable security, compliance assurance avoiding regulatory penalties, and competitive advantage from freeing technical talent for innovation.
Frame the initiative as mandatory compliance rather than optional optimization. The CA/Browser Forum’s mandate means organizations must implement automation regardless of internal preferences. The question becomes whether to prepare proactively or scramble reactively when deadlines approach. Proactive preparation minimizes costs and risks compared to rushed implementation.
Cross-Functional Team Assembly
Certificate management affects multiple organizational functions requiring coordination throughout implementation. Assemble cross-functional teams including security personnel who manage certificate policies and CA relationships, operations staff who deploy and maintain production systems, development teams who build and maintain applications, network engineers who configure load balancers and firewalls, and project managers who coordinate activities and track progress.
Define clear roles and responsibilities to prevent confusion about ownership. Ambiguity about who handles certificate renewals creates gaps where certificates expire because everyone assumed someone else would handle them. Document responsibility matrices specifying who performs each task, who approves decisions, who gets consulted, and who receives information.
Regular communication cadences keep teams aligned throughout implementation. Weekly status meetings during active implementation phases ensure issues surface quickly. Monthly steering committee meetings with leadership provide escalation paths for significant decisions or roadblocks.
Current State Assessment and Gap Analysis
Understanding current certificate management maturity establishes baseline conditions and identifies improvement opportunities. Comprehensive assessments examine certificate inventory completeness, renewal process automation levels, policy enforcement mechanisms, monitoring and alerting capabilities, and staff skills and training needs.
Gap analysis compares current state against target state requirements. For 47-day certificate lifetimes, target state requires complete certificate inventory automation, fully automated issuance and renewal, automated deployment to all systems, comprehensive monitoring and alerting, and documented procedures and trained staff.
Prioritize gaps based on business impact and implementation difficulty. Address high-impact, easy-to-implement items first for quick wins that build momentum. Save complex, lower-impact items for later phases when teams have developed expertise and confidence.
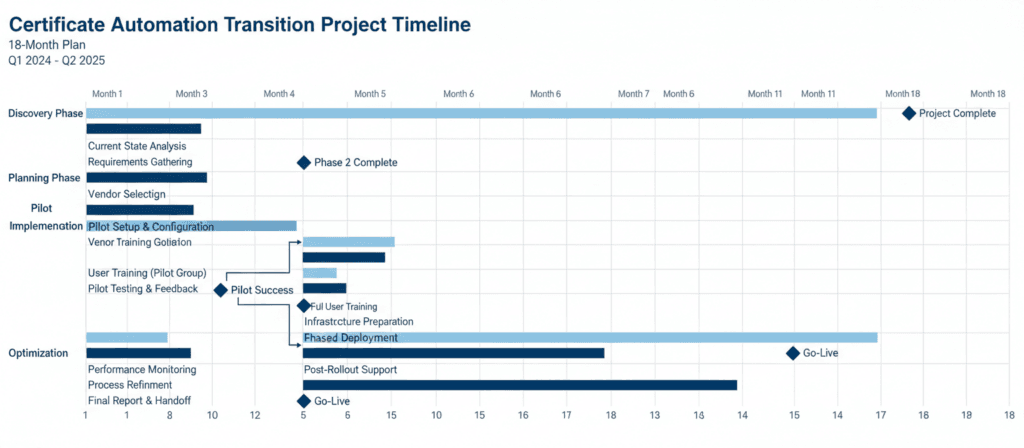
Immediate Actions (Months 1-3)
- Secure executive sponsorship
- Assemble cross-functional team
- Complete certificate discovery
- Document current processes
- Evaluate platform options
- Develop business case
- Create implementation roadmap
Near-Term Actions (Months 4-9)
- Select certificate management platform
- Conduct pilot implementations
- Develop automation workflows
- Train technical teams
- Create standard operating procedures
- Establish monitoring and alerting
- Begin production rollout
Long-Term Actions (Months 10-18)
- Complete production rollout
- Migrate legacy systems
- Optimize workflows
- Expand automation coverage
- Conduct post-implementation review
- Plan for future enhancements
- Prepare for subsequent mandates
Vendor Selection and Procurement
Choosing appropriate certificate management platforms and certificate authorities significantly impacts implementation success. Evaluation criteria should include technical capabilities matching your requirements, integration support for your specific infrastructure, vendor financial stability and longevity, customer support quality and availability, pricing models and total cost of ownership, and references from similar organizations.
Request detailed demonstrations focused on your specific use cases rather than generic product tours. Provide vendors with realistic scenarios from your environment and evaluate how well their solutions address your requirements. Test critical capabilities during proof-of-concept phases before committing to large purchases.
Negotiate contracts carefully, particularly regarding subscription terms and renewal conditions. Ensure pricing remains stable as your certificate volumes grow. Clarify support availability and response time commitments. Understand termination clauses and data portability in case you need to switch vendors later.
Training and Knowledge Transfer
Technical teams need training on new certificate management platforms, automation tools, and updated procedures. Different teams require different training depth based on their roles. Security teams need comprehensive platform administration training. Operations teams need training on troubleshooting automation failures. Development teams need training on integrating certificate automation into deployment pipelines.
Documentation supplements formal training by providing reference materials for ongoing operations. Standard operating procedures document routine tasks like requesting certificates for new services, investigating expiration alerts, and troubleshooting deployment failures. Runbooks document emergency procedures for handling critical certificate expirations or automation system failures.
Knowledge transfer from implementation specialists to internal teams ensures long-term sustainability. If external consultants assist with implementation, structure engagements to include training components. Shadow experienced consultants during initial implementations, then have them shadow internal staff as they perform subsequent implementations independently.
Risk Management and Contingency Planning
Despite careful planning, issues will inevitably occur during transition. Risk management identifies potential problems proactively and develops mitigation strategies. Common risks include automation platform failures or bugs, certificate authority availability issues, integration problems with legacy systems, resource constraints causing timeline delays, and resistance to change from affected teams.
Contingency plans define responses when risks materialize. Maintain emergency manual procedures for critical certificates in case automation fails. Establish relationships with multiple certificate authorities to enable failover if one becomes unavailable. Document rollback procedures if automation deployments cause problems. Maintain buffer time in implementation schedules to accommodate unexpected delays.
Regular risk reviews throughout implementation help teams stay ahead of emerging issues. Weekly team meetings should include risk discussion segments. Maintain risk registers tracking identified risks, mitigation actions, and ownership. Escalate significant risks that teams cannot resolve independently to steering committees or executive sponsors.
Common Implementation Challenges and Solutions
Organizations implementing certificate automation encounter predictable challenges. Learning from common pitfalls and proven solutions accelerates implementation while avoiding costly mistakes. This section examines frequent obstacles and practical approaches for overcoming them.
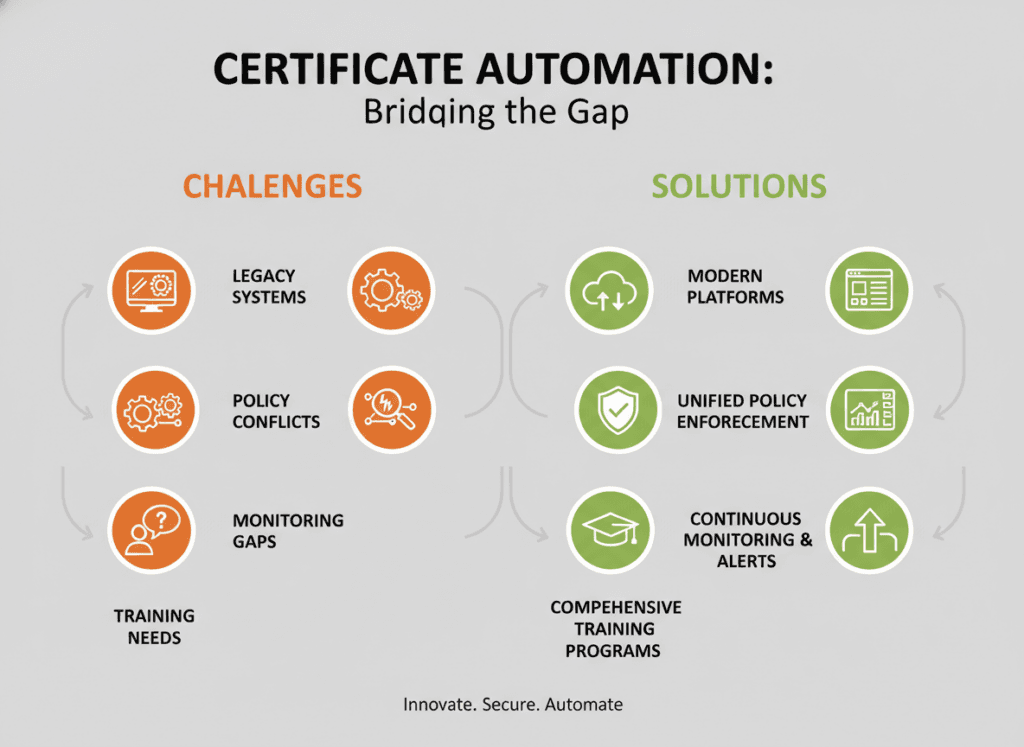
Legacy System Automation Difficulties
Older systems often lack native automation support, creating significant challenges for certificate management modernization. Legacy applications may require manual certificate installation through outdated management interfaces. Proprietary systems might use non-standard certificate formats or storage mechanisms incompatible with modern automation tools.
Several approaches address legacy system automation challenges. Reverse proxy placement in front of legacy systems centralizes TLS termination at the proxy layer. Modern proxies support automation while protecting unchanged legacy applications. This architecture requires network configuration changes but avoids modifying legacy applications directly.
API development provides programmatic certificate installation capabilities for systems lacking them. Custom scripts or middleware can accept certificates via APIs and handle installation using system-specific methods. While requiring development effort, this approach enables automation without replacing entire legacy systems.
Scheduled replacement planning recognizes that some systems cannot be effectively automated. For truly obsolete systems approaching end-of-life, organizations might choose to replace them rather than investing in automation workarounds. Certificate automation initiatives can accelerate replacement timelines by highlighting legacy system limitations.
Certificate Discovery Completeness
Many organizations discover they have far more certificates than initially believed. Shadow IT, forgotten development environments, and decentralized certificate procurement create situations where comprehensive certificate inventories don’t exist. Incomplete discovery leads to certificates expiring unexpectedly because they weren’t included in automation systems.
Continuous discovery processes rather than one-time scanning improve inventory completeness. Schedule regular network scans to identify new certificates as they appear. Integrate certificate inventory systems with configuration management databases to cross-reference known systems against discovered certificates.
Multiple discovery techniques improve coverage. Network scanning identifies certificates on systems accepting connections. Agent-based discovery finds certificates on systems running software agents. Log analysis discovers certificates mentioned in application logs. DNS monitoring tracks certificate-protected services through DNS queries. Combining approaches provides more comprehensive visibility than any single technique.
Policy Enforcement and Exception Handling
Strict certificate policies sometimes conflict with practical business needs. Development teams might need test certificates quickly without lengthy approval processes. Legacy systems might only support older cryptographic parameters incompatible with current policies. Emergency situations might require bypassing normal procedures.
Tiered policies accommodate different requirements across organizational environments. Production systems might require strict policies including manual approval, long cryptographic keys, and specific certificate authorities. Development environments might use relaxed policies allowing self-service issuance, shorter keys, and internal CAs. This flexibility balances security with operational efficiency.
Documented exception processes handle situations requiring policy deviations. Define clear criteria for when exceptions are appropriate, approval authority for granting exceptions, time limits on exception validity, and documentation requirements for audit purposes. Exceptions should be temporary whenever possible, with plans for remediating the underlying need.
Technical Challenges
- Legacy system incompatibility: Reverse proxies, API development, scheduled replacement
- Incomplete certificate discovery: Continuous scanning, multiple discovery methods
- Complex network environments: Distributed automation agents, federated management
- Integration limitations: Custom middleware, API development, vendor engagement
- Monitoring gaps: Comprehensive instrumentation, alert tuning
Organizational Challenges
- Resistance to change: Executive sponsorship, change management, training
- Resource constraints: Phased implementation, external assistance, priority management
- Unclear ownership: RACI matrices, documented procedures, regular reviews
- Policy conflicts: Tiered policies, exception processes, regular reviews
- Skills gaps: Comprehensive training, vendor support, knowledge transfer
Monitoring and Alerting Optimization
Effective monitoring requires balancing comprehensive coverage against alert fatigue. Too few alerts mean problems go undetected until they cause outages. Too many alerts, especially false positives, cause teams to ignore or disable alerting systems.
Tiered alerting routes different severity levels appropriately. Critical alerts indicating imminent certificate expirations on production systems go to on-call staff immediately. Warning alerts about certificates expiring in coming weeks route to team queues during business hours. Informational notifications about successful renewals go to monitoring dashboards without generating notifications.
Alert tuning based on operational experience reduces false positives over time. Track which alerts proved actionable versus which caused unnecessary interruptions. Adjust thresholds, add context to alerts, or consolidate related alerts based on lessons learned. Regular alert review sessions help teams continuously improve monitoring effectiveness.
Coordination With Change Management
Organizations with mature IT service management practices require change approval for production modifications. Certificate renewals technically constitute changes, potentially requiring approval for each renewal. At 47-day lifetimes, this creates untenable approval workload.
Pre-approved standard changes handle routine certificate renewals without individual approvals. Work with change management teams to classify automated certificate renewals as standard changes. Document the automation process, demonstrate reliability through pilot phases, and establish monitoring that would detect problems. Once approved as standard changes, routine renewals can proceed automatically with periodic reporting to change management for oversight.
Emergency change procedures handle situations requiring immediate certificate replacement outside normal schedules. Document clear criteria for emergency changes, streamlined approval processes, and post-implementation review requirements. Emergency procedures should be used rarely for genuine emergencies, not routinely to bypass standard processes.
Skills Development and Knowledge Retention
Certificate automation requires new skills that teams may not possess initially. Understanding certificate concepts, learning automation platforms, troubleshooting integration issues, and operating monitoring systems all require training and experience. Additionally, knowledge retention becomes challenging as staff turnover occurs.
Comprehensive training programs address initial skills gaps. Combine vendor-provided training with hands-on practice in test environments before attempting production implementations. Budget adequate time for learning curves, recognizing that initial implementations will take longer than subsequent ones.
Knowledge management practices preserve organizational learning despite staff changes. Maintain up-to-date documentation for all procedures. Record video demonstrations of complex processes. Conduct regular knowledge sharing sessions where experienced team members teach others. Create mentorship programs pairing experienced staff with new team members.
Post-Quantum Cryptography and Future Trends
The reduction to 47-day certificate lifetimes positions organizations to respond rapidly to emerging cryptographic threats and technology evolution. Understanding upcoming changes helps organizations prepare infrastructure that remains secure and compliant as the cryptographic landscape shifts.
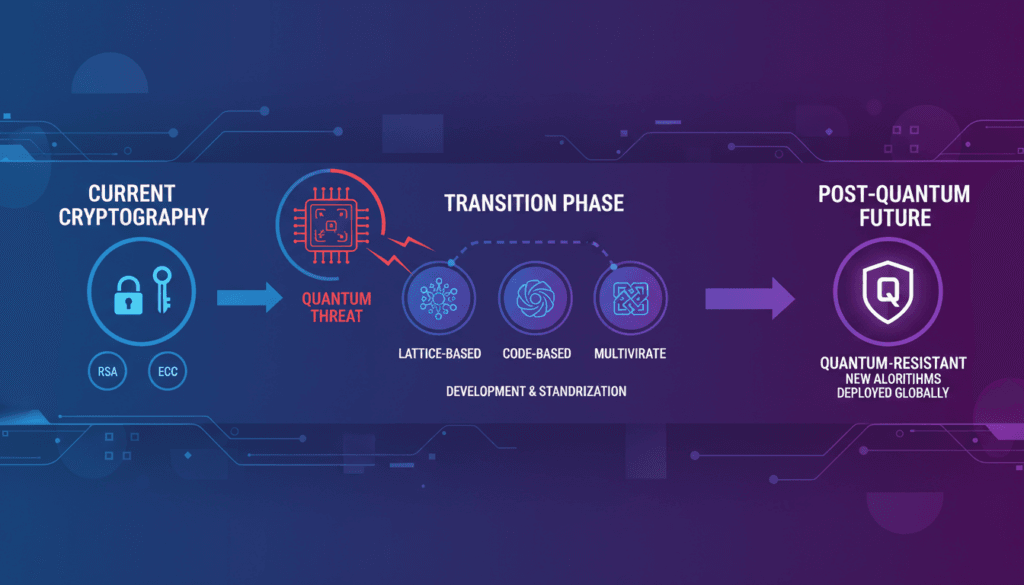
The Quantum Computing Threat to Current Cryptography
Quantum computers exploit quantum mechanical properties to solve certain mathematical problems exponentially faster than classical computers. Shor’s algorithm, running on sufficiently powerful quantum computers, can break the RSA and elliptic curve cryptography that currently protects TLS certificates and secure connections.
While practical quantum computers capable of breaking current cryptography don’t exist yet, significant research progress continues. Governments and technology companies invest billions in quantum computing development. Experts debate whether 10, 20, or 30 years remain before quantum computers threaten production cryptographic systems, but consensus holds that the threat is real and approaching.
Harvest now, decrypt later attacks pose immediate risks despite quantum computers remaining theoretical. Adversaries could capture encrypted traffic today and store it for future decryption once quantum computers become available. Data that must remain confidential for decades faces threats from this attack model even before quantum computers actually exist.
Post-Quantum Cryptographic Algorithm Development
The National Institute of Standards and Technology leads efforts to standardize quantum-resistant cryptographic algorithms. After years of evaluation, NIST selected several algorithms for standardization including CRYSTALS-Kyber for key encapsulation, CRYSTALS-Dilithium for digital signatures, and Falcon as an alternative signature scheme.
These algorithms use mathematical problems believed resistant to both classical and quantum computer attacks. Rather than relying on integer factorization or discrete logarithms like current algorithms, post-quantum cryptography uses lattice-based problems, code-based cryptography, or hash-based signatures. The underlying mathematical structures appear difficult for quantum algorithms to solve efficiently.
Implementation challenges accompany post-quantum algorithm adoption. New algorithms require larger key sizes and certificate sizes than current cryptography. Computational requirements differ, potentially affecting performance on resource-constrained devices. Protocol implementations must be updated to support new algorithm identifiers and parameters.
Cryptographic Agility and Migration Planning
Transitioning the entire internet to post-quantum cryptography represents a massive undertaking comparable to the HTTPS migration or IPv6 adoption. Unlike those transitions which could proceed gradually over years, quantum threats might emerge suddenly if quantum computing breakthroughs occur unexpectedly.
Short certificate lifetimes enable rapid cryptographic migration. Organizations with 47-day certificate renewal cycles can execute algorithm transitions within months. Certificate authorities can begin issuing certificates with post-quantum algorithms, and through normal renewal processes, the entire certificate ecosystem migrates quickly.
Cryptographic agility means designing systems to switch algorithms without fundamental architectural changes. Rather than hard-coding specific algorithms, implementations should support multiple algorithm families. Configuration changes rather than code modifications should enable algorithm transitions. This flexibility becomes critical as cryptographic landscapes evolve.
Migration Readiness: Organizations should prepare for post-quantum migration by ensuring certificate management systems support algorithm flexibility, verifying that infrastructure can handle larger certificate sizes, testing application compatibility with new algorithms, and developing migration playbooks before urgency forces rushed transitions.
Hybrid Cryptographic Approaches
Hybrid cryptography combines classical and post-quantum algorithms to provide protection against both current and future threats. TLS connections might use both ECDSA and Dilithium signatures, or both ECDH and Kyber for key exchange. Hybrid approaches protect against scenarios where post-quantum algorithms prove weaker than expected while also providing quantum resistance.
Certificate authorities are beginning to offer hybrid certificates containing both classical and post-quantum public keys and signatures. These certificates work with clients supporting post-quantum cryptography while maintaining backward compatibility with legacy clients. Hybrid approaches enable gradual ecosystem transition without requiring simultaneous upgrades everywhere.
Performance implications require careful evaluation. Hybrid approaches necessarily consume more bandwidth and processing power than single-algorithm approaches. Organizations must balance security benefits against performance impacts, particularly for high-volume systems or resource-constrained devices.
Evolution Beyond 47-Day Lifetimes
The certificate industry continues pushing toward shorter lifetimes even beyond 47 days. Some industry participants advocate for daily certificate rotation or even shorter. Short-lived certificates with seven-day or one-day validity periods already exist, exempted from revocation requirements due to their brief lifetimes.
Shorter lifetimes provide stronger security guarantees but demand more robust automation. Daily certificate rotation requires extremely reliable automation infrastructure with comprehensive monitoring and rapid incident response capabilities. Organizations must weigh security benefits against operational complexity.
The long-term trend points toward certificates as ephemeral credentials rather than long-lived trust anchors. This philosophical shift treats certificates more like session tokens than identity documents. While organizationally disruptive, this evolution arguably better aligns with modern zero-trust security architectures that continuously verify rather than persistently trust.
Industry Compliance and Regulatory Considerations
Certificate management intersects with numerous compliance frameworks and regulatory requirements across industries. Understanding these relationships helps organizations position certificate automation as compliance enablement rather than merely technical infrastructure improvement.
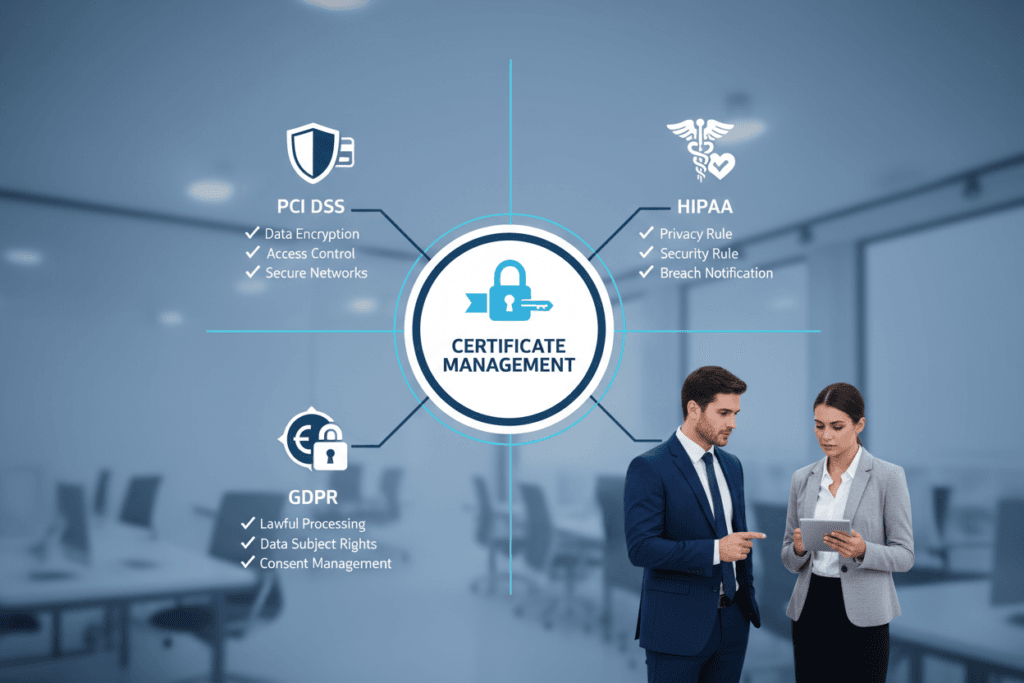
PCI DSS Certificate Requirements
The Payment Card Industry Data Security Standard mandates strong cryptography for protecting cardholder data transmission across networks. TLS certificates secure these transmissions, making proper certificate management essential for PCI DSS compliance. Requirements specify strong cipher suites, current protocol versions, and valid certificates without expiration.
PCI DSS audit processes examine certificate inventory, validate absence of expired certificates, confirm cryptographic strength, and review certificate management procedures. Automated certificate management with comprehensive audit logging substantially simplifies PCI DSS audits by providing documented evidence of continuous compliance.
Short certificate lifetimes can actually improve PCI DSS compliance posture. Frequent certificate rotation ensures cryptographic parameters remain current with evolving standards. Automated renewal eliminates human error that might allow certificates to expire. Comprehensive monitoring demonstrates continuous security maintenance rather than point-in-time compliance.
GDPR and Data Protection Requirements
The General Data Protection Regulation requires appropriate technical measures to protect personal data. While GDPR doesn’t explicitly mandate TLS certificates, encryption in transit represents a fundamental technical safeguard. Organizations processing EU citizen data must demonstrate appropriate encryption implementation.
GDPR compliance documentation should include certificate management policies, encryption protocol standards, certificate lifecycle procedures, and evidence of continuous security maintenance. Automated certificate management provides comprehensive audit trails demonstrating ongoing compliance rather than periodic compliance verification.
Data breach notification requirements create additional certificate management implications. If certificate expiration or compromise leads to data exposure, GDPR requires notification within 72 hours. Automated monitoring and alerting help organizations detect and respond to certificate issues before they escalate to reportable breaches.
HIPAA Security Rule Compliance
The Health Insurance Portability and Accountability Act Security Rule requires covered entities to implement technical safeguards for electronic protected health information. Encryption in transit represents an addressable implementation specification that most organizations implement through TLS certificates.
HIPAA audits examine whether organizations conducted risk analyses, implemented appropriate safeguards based on those analyses, and maintain security management processes. Certificate management documentation should demonstrate systematic approaches to certificate lifecycle management, not ad-hoc processes prone to failure.
Shorter certificate lifetimes align well with HIPAA’s emphasis on technical safeguard maintenance and improvement. Regular certificate rotation demonstrates ongoing security program activity. Automated management reduces risks of human error that might compromise protected health information.
| Compliance Framework | Certificate Requirements | Audit Considerations | Automation Benefits |
| PCI DSS | Strong encryption for cardholder data transmission, valid unexpired certificates, approved cipher suites | Certificate inventory, expiration monitoring, cryptographic strength validation | Continuous compliance evidence, elimination of expiration risk, cryptographic currency |
| GDPR | Appropriate technical measures for personal data protection, encryption in transit | Security measure documentation, breach prevention evidence, technical safeguard implementation | Comprehensive audit trails, demonstrated ongoing security, breach prevention |
| HIPAA | Technical safeguards for ePHI transmission, addressable encryption specifications | Risk analysis documentation, implemented safeguards, security management processes | Systematic lifecycle management, reduced human error, documented processes |
| SOC 2 | Security principle controls, encryption implementation, certificate lifecycle management | Control design effectiveness, operating effectiveness, continuous monitoring | Control automation, continuous monitoring evidence, consistent execution |
| ISO 27001 | Information security controls including cryptography, key management procedures | Documented ISMS procedures, control implementation, continuous improvement | Documented procedures, consistent control execution, measurement and improvement |
SOC 2 Trust Services Criteria
Service Organization Control 2 reports evaluate controls related to security, availability, processing integrity, confidentiality, and privacy. Many criteria relate directly or indirectly to certificate management, particularly within the security and confidentiality principles.
SOC 2 auditors assess control design and operating effectiveness. Manual certificate management creates operating effectiveness risks because consistent execution depends on human performance. Automated certificate management strengthens operating effectiveness by ensuring controls execute reliably without human error.
Monitoring and measurement form key components of SOC 2 compliance. Automated certificate management systems provide comprehensive metrics on renewal success rates, time to remediation for failures, and certificate inventory accuracy. These metrics demonstrate continuous control operation rather than point-in-time compliance.
Industry-Specific Regulations
Various industries face additional regulatory requirements beyond common frameworks. Financial services organizations must comply with regulations from banking authorities, securities regulators, and financial system overseers. Healthcare organizations face state-level privacy laws supplementing federal HIPAA requirements. Government contractors must meet Federal Risk and Authorization Management Program requirements.
Industry regulations increasingly emphasize continuous security rather than periodic assessments. Traditional audit approaches evaluated point-in-time compliance, but modern regulations recognize security as ongoing processes. Short certificate lifetimes with automated management align perfectly with continuous compliance models.
Regulatory harmonization benefits from standardized certificate management. Organizations operating across multiple jurisdictions or industries can implement consistent certificate management satisfying various regulatory requirements simultaneously. This efficiency reduces compliance costs while maintaining or improving security postures.
Frequently Asked Questions
Why did the CA/Browser Forum choose 47 days specifically instead of a rounder number?
The 47-day period follows a mathematical formula: one maximum-length month (31 days) plus half of a standard month (15 days) plus one day of buffer time. This calculation provides a practical time window that accommodates the longest possible month while allowing reasonable buffer for certificate renewal processes. The same formula scaled differently produced the 200-day and 100-day intermediate milestones, maintaining consistent proportional relationships throughout the transition phases.
Will certificate costs increase with more frequent renewals?
No, certificate costs should not increase due to renewal frequency. Most commercial certificate authorities charge based on annual subscriptions that cover unlimited reissuances within the subscription period. Whether you renew certificates twice or eight times during the year, the certificate authority fees remain constant. The real cost consideration involves labor for manual management versus investment in automation platforms. Organizations that automate typically find their total certificate management costs decrease despite shorter lifetimes.
Can I continue using manual certificate management with 47-day lifetimes?
Technically possible but practically infeasible for most organizations. Manual management of even moderate certificate portfolios at 47-day lifetimes requires unsustainable labor investment. Additionally, the domain validation reuse period drops to just 10 days, making manual revalidation extremely burdensome. The CA/Browser Forum explicitly acknowledged that automation becomes mandatory rather than optional at 47-day lifetimes. Organizations attempting manual management at this frequency will likely experience frequent certificate expirations, service outages, and overwhelming staff workload.
What is ACME Renewal Information and why does it matter?
ACME Renewal Information is a protocol extension that allows certificate authorities to communicate optimal renewal timing for each specific certificate. Rather than using fixed renewal windows, ARI enables CAs to recommend renewing certain certificates earlier due to planned maintenance, security concerns, or load distribution needs. At 47-day lifetimes, renewal timing becomes increasingly critical. Renewing too early wastes valid certificate days, while renewing too late risks expiration if problems occur. ARI helps optimize renewal timing based on CA-specific operational knowledge, improving both security and efficiency.
How do short certificate lifetimes help with post-quantum cryptography migration?
Short certificate lifetimes enable rapid cryptographic transitions across the entire internet. When quantum computers threaten current encryption algorithms, the industry will need to migrate to post-quantum cryptography quickly. With 47-day certificate lifetimes, certificate authorities can begin issuing certificates using quantum-resistant algorithms, and through normal renewal cycles, the entire ecosystem transitions within months rather than years. This cryptographic agility becomes increasingly important as quantum computing research progresses and new cryptographic threats emerge.
What happens to my existing certificates when deadlines arrive?
Existing certificates remain valid until their natural expiration dates regardless of when implementation deadlines arrive. The new maximum lifetime requirements only apply to certificates issued after each deadline date. For example, a certificate issued for 398 days on March 14, 2026, remains valid for its full term even though certificates issued on March 15, 2026, cannot exceed 200 days. However, organizations should plan automation implementation before deadlines to ensure renewal processes are ready when existing certificates expire.
Do shorter lifetimes really improve security or just create operational burden?
Shorter lifetimes provide genuine security improvements beyond operational changes. They limit the exposure window if private keys are compromised, enforce regular cryptographic key rotation, ensure certificate information remains current, reduce dependency on unreliable revocation systems, and enable rapid response to cryptographic vulnerabilities. The CA/Browser Forum extensively documented these security benefits in the ballot justification. While shorter lifetimes do create operational challenges, automation effectively addresses these challenges while preserving the security benefits.
How do I handle certificate management for legacy systems that don’t support automation?
Several approaches address legacy system automation challenges. Placing reverse proxies or load balancers in front of legacy systems centralizes TLS termination at the proxy layer where automation is supported. Developing custom APIs or middleware can provide programmatic certificate installation for systems lacking native automation support. For systems approaching end-of-life, accelerating replacement timelines might prove more cost-effective than developing elaborate automation workarounds. The specific approach depends on the system’s criticality, remaining lifespan, and technical architecture.
Conclusion: Embracing Mandatory Automation
The formal reduction of TLS certificate lifetimes to 47 days represents far more than a technical specification change. This mandate fundamentally transforms how organizations approach certificate lifecycle management, forcing a shift from manual processes to comprehensive automation. The transition timeline provides adequate preparation time, but only for organizations that begin planning and implementation immediately.
Understanding the security motivations behind this change helps organizations move beyond viewing it as mere compliance burden. Shorter certificate lifetimes meaningfully improve internet security by limiting cryptographic key exposure, enforcing regular rotation, ensuring information currency, and enabling rapid cryptographic transitions. These benefits strengthen security postures while creating operational challenges that automation effectively addresses.
The business case for certificate automation extends beyond compliance necessity. Organizations implementing comprehensive automation realize substantial cost savings through reduced labor requirements, eliminated outage risks, improved compliance efficiency, and redirected technical talent toward strategic initiatives. Most organizations achieve return on automation investment within 12-18 months, with continuing benefits indefinitely thereafter.
Successful implementations require more than just technology deployment. Organizations need executive sponsorship, cross-functional coordination, comprehensive planning, phased implementation approaches, and ongoing optimization. Treating certificate automation as strategic infrastructure transformation rather than tactical technology implementation produces superior long-term results.
Action Timeline: Organizations should complete certificate discovery and planning by Q3 2025, select and implement automation platforms by Q2 2026, and achieve primary system automation before the March 2026 deadline. This timeline provides adequate buffer for addressing unexpected challenges while ensuring readiness before mandatory compliance dates.
The path forward is clear. Manual certificate management cannot scale to 47-day renewal cycles for any organization managing more than a handful of certificates. Automation is not optional but mandatory. The only strategic question involves whether organizations prepare proactively or scramble reactively when deadlines force action.
Organizations beginning preparation now enjoy significant advantages. They can select optimal automation platforms without time pressure, implement thoughtfully without rushing, learn from pilot deployments before production rollout, and arrive at deadlines with proven, stable automation rather than untested emergency implementations.
The certificate industry’s evolution toward shorter lifetimes will likely continue beyond 47 days. Organizations building robust automation infrastructure position themselves advantageously for future requirements. The automation capabilities developed for 47-day certificates will serve organizations well as lifetime requirements potentially decrease further.
This transformation ultimately strengthens internet security for everyone. While individual organizations may find transition challenging, the collective impact improves cryptographic practices, reduces compromise exposure, and prepares the ecosystem for emerging threats like quantum computing. Organizations should view their automation initiatives as contributions to broader internet security improvement.
Begin Your Certificate Automation Journey Today
Don’t wait until deadlines force rushed implementation. Our certificate management specialists can guide you through every step of the automation transition, from initial discovery and planning through platform selection, implementation, and optimization. With proven methodologies and extensive experience across diverse environments, we help organizations achieve smooth transitions that enhance security while minimizing business disruption.


